Privilege Review in eDiscovery: Workflow, Redaction, and Defensibility
by Ali Rind, Last updated: May 12, 2026, ref:

Privileged and confidential information in discovery refers to documents protected from production under attorney-client privilege, work product doctrine, or confidentiality obligations. Mishandling these materials carries real consequences: privilege waiver, court sanctions, fee-shifting, and in serious cases malpractice exposure. The volume of modern discovery makes the problem harder, with productions running into hundreds of thousands of documents and review teams under deadline pressure.
This guide walks through what counts as privileged, where privilege handling fits in the discovery workflow, how to build a defensible privilege log, how redaction gets executed in practice, and what protections exist when something goes wrong.
What Counts as Privileged or Confidential in Discovery
Not every sensitive document is privileged, and not every privileged document gets withheld. Understanding the categories matters because each carries different protection levels and different production obligations.
-
Attorney-client privilege protects confidential communications between a lawyer and client made for the purpose of seeking or providing legal advice. It is the oldest and most absolute of the protections, but it is also the most commonly misunderstood. A communication is not privileged simply because a lawyer was copied on it, and business advice from in-house counsel typically does not qualify even when the lawyer is the sender.
- Work product doctrine, codified in FRCP 26(b)(3), protects materials prepared in anticipation of litigation or for trial. Unlike attorney-client privilege, work product can be created by non-lawyers acting at the direction of counsel, including paralegals, investigators, and consulting experts. The doctrine distinguishes between fact work product, which can be obtained on a showing of substantial need, and opinion work product, which receives near-absolute protection because it reveals the attorney's mental impressions and strategy.
-
Common interest privilege, sometimes called joint defense privilege, extends attorney-client protection to communications shared between parties with aligned legal interests. It applies in co-defendant scenarios and certain transactional contexts, but breaks the moment the parties' interests diverge.
-
Trade secrets and confidential business information are not strictly privileged but are routinely protected through protective orders and confidentiality designations such as "Confidential" or "Attorneys' Eyes Only." These documents typically get produced with redactions rather than withheld entirely.
The critical distinction to internalize: privileged documents are withheld from production and logged. Confidential documents are produced under protective order, often with redactions covering the most sensitive content.
The Four Privilege Types Lawyers Encounter Most Often
Attorney-Client Privilege
For attorney-client privilege to apply, four elements must be present: a communication, made in confidence, between attorney and client (or their representatives), for the purpose of obtaining or providing legal advice. The privilege belongs to the client, not the attorney, and only the client can waive it.
The most common pitfalls in modern practice involve dilution through wide distribution. When a privileged email is forwarded to non-lawyer business staff who do not need the legal advice to perform their roles, privilege can be lost. Similarly, communications that mix legal advice with business strategy create ambiguity that opposing counsel will exploit during privilege challenges.
Work Product Doctrine
The work product doctrine originated in Hickman v. Taylor and now lives in FRCP 26(b)(3). It protects two tiers of material with different standards.
Fact work product covers materials gathered or organized in anticipation of litigation: witness statements, document compilations, factual investigation memos. Opposing counsel can obtain fact work product by showing substantial need and undue hardship in obtaining the equivalent elsewhere.
Opinion work product covers the mental impressions, conclusions, opinions, and legal theories of an attorney or representative. It receives much stronger protection and is rarely ordered produced.
Common Interest Privilege
Common interest privilege allows parties with aligned legal interests to share privileged information without waiving privilege. It applies to co-defendants in litigation, parties in joint ventures facing common legal exposure, and certain insurer-insured relationships. The doctrine is jurisdiction-sensitive. Some courts require active litigation; others permit common interest in anticipated litigation or transactional contexts. The privilege evaporates the moment the parties' interests diverge.
Trade Secret and Confidential Information
Trade secrets and confidential commercial information receive protection through protective orders rather than evidentiary privilege. The standard mechanism is a two-tier protective order with "Confidential" and "Attorneys' Eyes Only" designations. Confidential materials can be shared with the receiving party's in-house counsel and litigation team. AEO materials are restricted to outside counsel and approved experts, preventing competitive exposure.
Where Privilege Handling Fits in the eDiscovery Workflow
The Electronic Discovery Reference Model (EDRM) breaks discovery into stages: identification, preservation, collection, processing, review, analysis, production, and presentation. Privilege handling spans the back half of this workflow, but the decisions made early shape how painful the later stages become.
During identification, custodian interviews and scope definitions determine which document populations carry the highest privilege risk. Legal department employees, in-house counsel, and external advisor communications get flagged as elevated-risk custodians from the start.
Processing introduces deduplication, metadata extraction, and email threading. Privilege-aware processing keeps email families together so that a parent message and its attachments move through review as a unit. This prevents the common error of producing an attachment whose parent email was withheld for privilege.
Review is where privilege determinations happen. The standard workflow uses a two-pass model. First-pass reviewers, often contract attorneys or paralegals, tag documents as potentially privileged using search term lists and judgment. Second-pass senior attorneys verify the calls and finalize the privilege determination.
Production is where redactions get applied and the privilege log gets generated. By the time documents reach production, privilege calls should be settled. Last-minute privilege discoveries during production are a sign the review workflow upstream needs strengthening.
The Four-Stage Privilege Workflow
Stage 1: Identify
Identification combines search term lists, custodian-based filters, and pattern recognition. Effective search term lists include the names of every attorney involved in the matter, law firm email domains, common legal-advice trigger phrases such as "privileged and confidential" or "attorney work product," and case-specific terminology. Lists are built collaboratively with the case team, not assembled in isolation by the eDiscovery vendor.
AI-enhanced search across documents, audio, and video can pre-flag potentially privileged materials before attorney review begins, scanning for names, entities, and trigger phrases at volume. This shifts the workload from "review everything and tag privileged" to "review the flagged subset and confirm or override."
Stage 2: Review
First-pass reviewers handle volume. Senior attorneys handle judgment. The hardest calls are mixed-purpose communications where legal advice and business advice intertwine, and communications copied to non-lawyers whose role in the legal matter is ambiguous.
Quality control through sampling is non-negotiable. A random sample of first-pass calls gets verified by senior attorneys, and statistically significant error rates trigger remediation. Documented QA processes are part of the "reasonable steps" analysis under FRE 502(b) if anything goes wrong later.
Stage 3: Log
The privilege log is the record of every document withheld from production on privilege grounds. FRCP 26(b)(5)(A) requires the producing party to expressly claim privilege and describe the nature of the withheld material in a way that enables the receiving party to assess the claim.
Two formats are accepted. Document-by-document logs assign every withheld document its own row with full metadata. Categorical logs, endorsed by the Sedona Conference, group similar documents and describe categories rather than individuals. Categorical logs are appropriate for high-volume productions where document-by-document logging would be disproportionately burdensome.
Required fields in a defensible privilege log include the document date, author, all recipients (including blind copies), document type, privilege type asserted, and a description specific enough to support the claim without revealing the privileged content itself. The most common log mistake is generic description: writing "legal advice" instead of "email seeking legal advice from outside counsel regarding pending regulatory inquiry."
Stage 4: Redact or Withhold
The redact-or-withhold decision turns on what portion of the document is privileged. A document that is privileged in its entirety gets withheld and logged. A document with a privileged passage embedded in otherwise responsive content gets produced with that passage redacted. The redaction itself then needs to satisfy production requirements: visible blackout, permanently applied, underlying text removed, metadata scrubbed.
How Redaction Actually Gets Done in Discovery
Redaction is the bridge between privilege review and production. Decisions made during review become physical changes to documents, and execution quality determines whether those decisions actually hold.
Redaction targets in discovery extend beyond privileged communications: third-party PII like social security numbers and medical information, bank and financial account details, trade secrets and confidential business strategy, source code in software litigation, and irrelevant private content from personal email custodians.
Manual redaction breaks down at scale. A careful reviewer might handle fifty pages per hour on simple documents. A hundred-thousand-page production becomes two thousand reviewer-hours of work, and as deadlines compress, error rates climb. The classic failure is the redaction that is not really one: a black rectangle drawn over PDF text that leaves the underlying content selectable, searchable, and visible in the file's metadata. Opposing counsel discovers the leak with one keyboard shortcut.
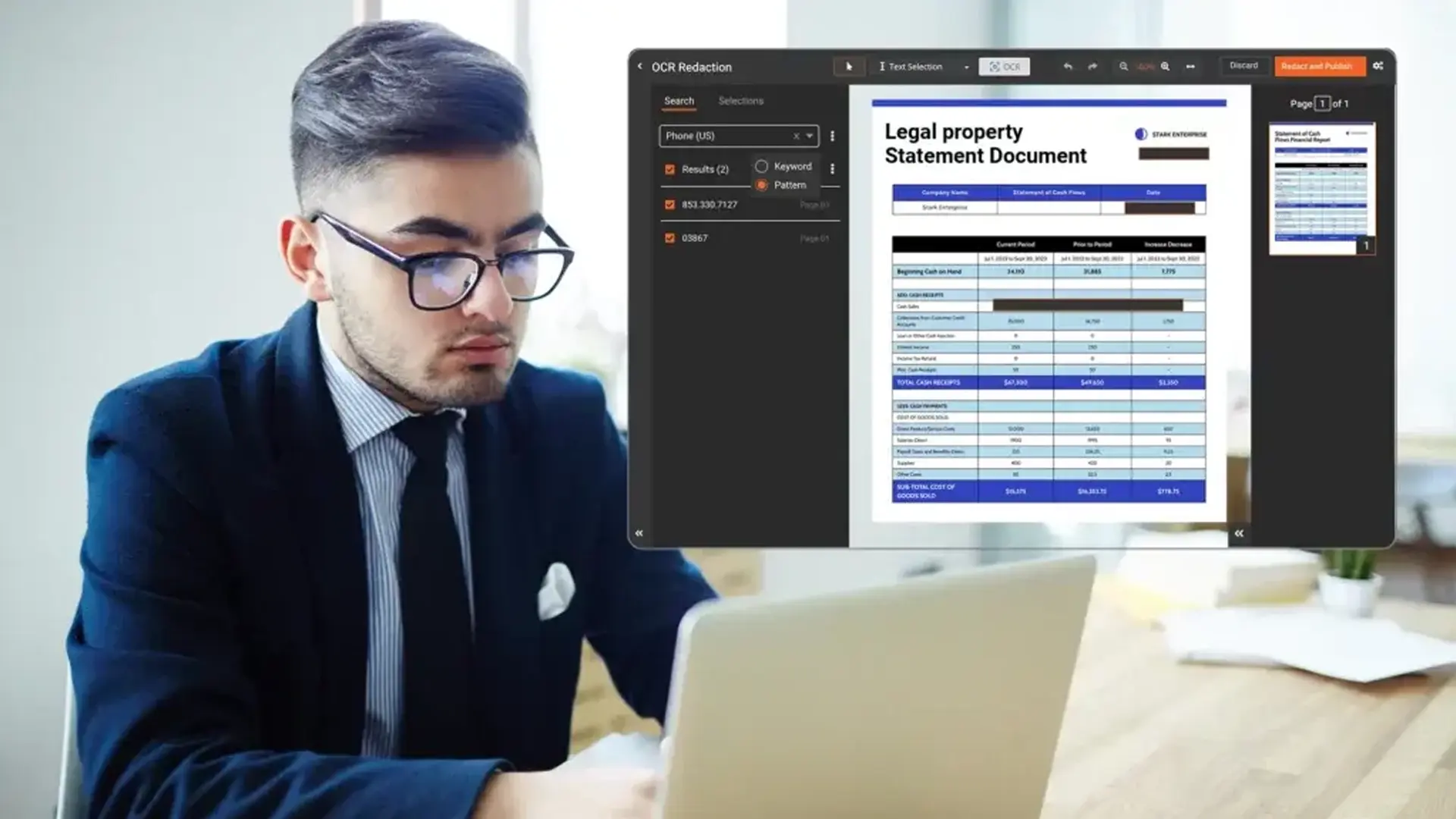
The defensible model is AI-assisted redaction with human verification. Pattern-based redaction handles structured PII reliably, AI-powered object detection covers names and entities across documents and images, and bulk processing applies redactions across thousands of files in the time manual review would spend on a hundred. The judgment calls (privilege determinations, legal-versus-business advice, partial-redact-versus-withhold) stay with attorneys, supported by manual redaction controls for verification and edge cases.
What to look for in legal redaction software for discovery: permanent burn-in that removes underlying text rather than visually covering it, metadata scrubbing, audit trails and chain of custody logging, format support across PDF, Word, Excel, email, and images, bulk processing, and security certifications like SOC 2 and ISO 27001.
VIDIZMO Redactor combines automated PII and pattern detection with attorney review workflows and full audit trail logging across documents, images, audio, and video in a single platform.
Manual redaction at production scale invites the kind of mistake that ends in a waiver motion. VIDIZMO Redactor combines AI-powered detection, permanent burn-in, and full audit logging across documents, images, audio, and video, so privilege calls actually hold up. Contact us to see in action.
Consequences of Mishandling Privileged Documents
The waiver problem is what makes privilege handling consequential. A single inadvertently produced privileged document can, in some jurisdictions and on some facts, waive privilege over the entire subject matter. Subject matter waiver means that producing one privileged email about a transaction can compromise privilege over every other privileged document touching that transaction.
Sanctions for privilege failures range from fee-shifting and adverse inference instructions to evidentiary preclusion in serious cases. Beyond the litigation itself, repeated privilege failures expose the producing firm to malpractice claims from the client whose privileged communications were exposed.
The protective framework under Federal Rule of Evidence 502 limits these risks substantially.
FRE 502(b) protects against waiver when privileged material is inadvertently disclosed, provided three conditions are met: the disclosure was inadvertent, the holder took reasonable steps to prevent disclosure, and the holder took reasonable steps to rectify the error after discovery. Courts assess "reasonable steps" by looking at the scope of discovery, the procedures used to screen for privilege, and the diligence of the review. Multi-pass review, technology-assisted screening, and documented QA processes all strengthen the reasonable-steps argument.
FRE 502(d) lets parties obtain a court order specifying that disclosure of privileged information in the case does not waive privilege in any other federal or state proceeding. A 502(d) order negotiated at the Rule 26(f) conference is the strongest available protection and costs nothing to obtain.
Clawback agreements are contractual mechanisms between parties that establish the procedure for recovering inadvertently produced privileged documents. A typical clawback agreement specifies a notice procedure, return-or-destroy obligations, no-waiver language, and treatment of expert review of recalled documents. FRCP 26(b)(5)(B) provides the federal default procedure if no agreement exists, but a negotiated agreement gives both sides more clarity.
Practical Best Practices for Privilege Handling
Effective privilege workflows share common features regardless of matter size. Build search term lists collaboratively with the case team rather than in isolation, because the people closest to the facts know which attorneys, advisors, and trigger phrases matter. Then run pattern-based privilege screens before attorney review, not after, so review time gets spent on judgment calls rather than triage.
Treat the privilege log as a deliverable from day one rather than an end-of-production scramble. Capture metadata during review instead of reconstructing it later, and burn in redactions and scrub metadata as part of the production pipeline. Sampling-based QA catches failures before production goes out, and a negotiated 502(d) order and clawback agreement at the Rule 26(f) conference adds a layer of protection that costs nothing to obtain.
Privilege handling rewards systems thinking. The teams that handle it well treat it as a workflow problem solved through process and tooling, not a one-time review problem solved through heroic effort.
People Also Ask
In eDiscovery, "privileged" means a document is protected from production under a legal doctrine like attorney-client privilege or work product. Fully privileged documents are withheld and recorded on a privilege log. Documents that are only partially privileged get produced with the protected passages redacted.
Privileged documents are withheld from production entirely under legal doctrine. Confidential documents are produced under a protective order, usually with redactions covering the most sensitive content. Trade secrets, third-party PII, and regulated data are typically confidential rather than privileged.
A traditional linear review processes fifty to seventy-five documents per reviewer-hour, and manual redaction adds two to four hours per hundred pages. A hundred-thousand-document production can require two thousand reviewer-hours. AI-assisted screening and pattern-based redaction compress this timeline substantially.
No. AI handles pattern-based detection of PII, names, and trigger phrases reliably and can apply redactions across thousands of documents in bulk. What it does not replace are judgment calls on privilege, business-versus-legal advice, and redact-versus-withhold decisions. The defensible workflow combines AI screening with attorney verification.
A privilege log is the record of every document withheld from production on privilege grounds. FRCP 26(b)(5)(A) requires the producing party to claim privilege expressly and describe the withheld material in enough detail for the receiving party to assess the claim. Partially privileged documents get redacted and produced, not logged.
Inadvertent production does not automatically waive privilege. FRE 502(b) protects against waiver if the disclosure was inadvertent, reasonable steps were taken to prevent it, and the error was promptly rectified through a clawback notice. The most common cause is a redaction that visually covers text without removing the underlying content, which is why permanent burn-in matters.
About the Author
Ali Rind
Ali Rind is a Product Marketing Executive at VIDIZMO, where he focuses on digital evidence management, AI redaction, and enterprise video technology. He closely follows how law enforcement agencies, public safety organizations, and government bodies manage and act on video evidence, translating those insights into clear, practical content. Ali writes across Digital Evidence Management System, Redactor, and Intelligence Hub products, covering everything from compliance challenges to real-world deployment across federal, state, and commercial markets.
Jump to
You May Also Like
These Related Stories
Bulk Document Redaction for Law Firms: Redact Thousands of Documents

Best Redaction Systems for Subpoenas and Legal Demands



No Comments Yet
Let us know what you think