What Is HIPAA and Why Does It Matter for Data Redaction?
by Ali Rind, Last updated: April 2, 2026, ref:
The Health Insurance Portability and Accountability Act (HIPAA) is a US federal law enacted in 1996 that establishes national standards for protecting sensitive patient health information. It applies to covered entities (healthcare providers, health plans, and healthcare clearinghouses) and their business associates, requiring them to implement safeguards that prevent unauthorized access to, use of, or disclosure of protected health information (PHI).
For compliance officers, privacy teams, and records managers in healthcare, HIPAA isn't just a regulation. It's the operational baseline for every decision involving patient data. The penalties for getting it wrong are steep.
The US Department of Health and Human Services (HHS) Office for Civil Rights (OCR) has settled or imposed penalties in hundreds of cases since the enforcement rule took effect, with individual fines ranging from $100 to over $2 million per violation category. Between 2009 and 2022, more than 382 million healthcare records were exposed in reported breaches, according to data tracked by HIPAA Journal. That's why healthcare organizations treat PHI protection as an existential priority.
Key Takeaways
- HIPAA requires covered entities and business associates to protect 18 categories of protected health information (PHI) across all media types, including paper, digital, and verbal communications.
- PHI exists in places most organizations overlook: telehealth recordings, surgical videos, scanned intake forms, voicemails, and insurance claim files.
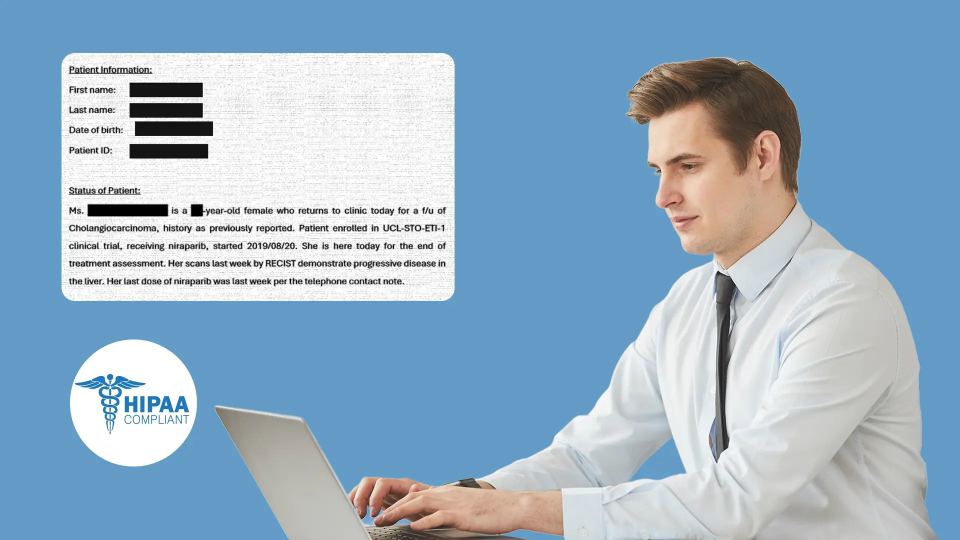
- Redaction is one of the most effective methods for creating HIPAA-safe versions of records that must be shared, published, or stored beyond their retention period.
- Manual redaction of multimedia PHI is slow, inconsistent, and difficult to audit, which creates compliance risk at scale.
- AI-powered redaction tools can detect and remove 40+ PHI types across documents, images, video, and audio in a single workflow.
What Does HIPAA Actually Require?
HIPAA requires organizations that handle health information to protect it from unauthorized disclosure. That sounds simple. In practice, the law's scope is broad, covering three major rule sets: the Privacy Rule, the Security Rule, and the Breach Notification Rule.
The Privacy Rule defines what counts as protected health information and sets limits on who can access it. It requires covered entities to provide patients with a Notice of Privacy Practices, obtain authorization before certain uses of PHI, and allow individuals to access and amend their records.
Under the Security Rule, organizations must protect electronic PHI (ePHI) specifically. That means administrative safeguards (risk assessments, workforce training, access management), physical safeguards (facility access controls, workstation security), and technical safeguards (encryption, audit controls, transmission security).
Then there's the Breach Notification Rule. When an unauthorized disclosure of unsecured PHI occurs, covered entities must notify affected individuals, HHS, and in some cases the media within 60 days of discovery. "Unsecured" here means PHI that hasn't been rendered unusable through encryption or destruction.
Who Must Comply with HIPAA?
HIPAA applies to two categories of organizations:
-
Covered entities: Healthcare providers who transmit health information electronically, health plans (insurers, HMOs, government programs like Medicare), and healthcare clearinghouses.
-
Business associates: Any organization that creates, receives, maintains, or transmits PHI on behalf of a covered entity. This includes cloud hosting providers, billing companies, transcription services, IT contractors, and redaction service vendors.
Business associates must sign a Business Associate Agreement (BAA) with each covered entity they serve. Without a BAA in place, sharing PHI with a vendor is itself a HIPAA violation.
What Counts as Protected Health Information?
PHI is any individually identifiable health information that relates to a person's past, present, or future health condition, treatment, or payment for healthcare. The HHS de-identification guidance specifies 18 identifier types that make health information "individually identifiable."
These 18 identifiers are:
- Names
- Geographic data smaller than a state
- Dates (except year) related to an individual
- Phone numbers
- Fax numbers
- Email addresses
- Social Security numbers
- Medical record numbers
- Health plan beneficiary numbers
- Account numbers
- Certificate/license numbers
- Vehicle identifiers and serial numbers
- Device identifiers and serial numbers
- Web URLs
- IP addresses
- Biometric identifiers (fingerprints, voiceprints)
- Full-face photographs and comparable images
- Any other unique identifying number, characteristic, or code
Here's the detail many organizations miss: PHI isn't limited to text in a database. A face visible in a surgical video is PHI. A patient's voice on a recorded telehealth call is PHI. A scanned intake form with a handwritten name is PHI. Any medium that contains identifiable health information falls under HIPAA's protection requirements.
Why Is HIPAA Compliance So Difficult for Multimedia Records?
Text-based PHI in structured databases is relatively straightforward to manage. Access controls, encryption, and database-level masking handle most scenarios. The challenge grows sharply when PHI lives inside unstructured content: video recordings, audio files, scanned documents, and medical images.
Consider a clinical trial sponsor reviewing surgical procedure videos for a research publication. Every frame where a patient's face, name band, or chart is visible must be redacted before the video can leave the organization. A single missed frame in a 45-minute recording can constitute a breach.
Or consider a healthcare call center. Patients routinely speak their Social Security numbers, dates of birth, prescription details, and insurance IDs during calls. If those recordings are shared with a quality assurance vendor or used for agent training, every spoken identifier must be removed first.
How Manual Redaction Creates Compliance Risk
Manual redaction of multimedia content is painfully slow. Redacting one hour of video footage can take eight or more analyst hours, depending on the density of identifiable content. For audio, an analyst must listen to every minute of every recording, mark each PHI instance, and apply muting or bleeping. That's time pulled directly from other compliance work.
Document redaction at scale is equally burdensome. Healthcare organizations processing thousands of pages per engagement (common in clinical trials and insurance claims) face weeks of manual review. Inconsistency is inevitable when multiple staff members apply redaction rules differently. And without a complete audit trail, there's no way to prove that redaction was performed correctly if a regulator comes asking.
How Do Organizations De-Identify PHI Under HIPAA?
HIPAA's Privacy Rule provides two approved methods for de-identifying health information, both defined under 45 CFR 164.514. Once information is properly de-identified, it's no longer considered PHI, and HIPAA restrictions on its use and disclosure no longer apply.
What Is the Expert Determination Method?
A qualified statistical or scientific expert applies methods to determine that the risk of identifying an individual from the data is "very small." The expert must document their analysis. This method is flexible but requires specialized expertise and can be expensive for large datasets.
What Is the Safe Harbor Method?
The organization removes all 18 identifier types listed above and has no actual knowledge that the remaining information could identify an individual. Safe Harbor is the more commonly used approach because it provides a clear, repeatable checklist. But it demands thoroughness: missing even one identifier type means the data isn't de-identified.
Redaction is the primary technical mechanism for achieving Safe Harbor de-identification in documents and multimedia. By physically removing or obscuring identifiers from files before sharing, organizations create versions that satisfy the 18-identifier removal requirement while preserving the underlying clinical or operational content.
What Should a HIPAA-Compliant Redaction Workflow Include?
Any organization using redaction to protect PHI needs a workflow that satisfies both the Privacy Rule's de-identification requirements and the Security Rule's technical safeguards. Here's what that looks like in practice.
Comprehensive Format Coverage
PHI doesn't live in just one file type. A single patient encounter might generate a PDF intake form, a video consultation recording, an audio voicemail, and a DICOM imaging file. The redaction workflow must handle all of these. Organizations that use separate tools for document redaction and video redaction create gaps where PHI can slip through during handoffs between systems.
Automated PHI Detection
Manual identification of PHI is error-prone at any volume beyond trivial. Effective workflows use AI-powered detection that can identify all 18 HIPAA identifier types across text (printed and handwritten), spoken language, and visual content (faces, name bands, ID badges). The detection engine should support pattern matching (for structured identifiers like SSNs and medical record numbers) and contextual AI recognition (for unstructured mentions of names, conditions, and locations).
Configurable Accuracy Controls
Not all PHI carries equal risk, and not all content requires the same level of scrutiny. A well-designed workflow lets teams configure confidence thresholds so they can balance thoroughness against false positive rates. High-stakes clinical trial documents might use a low threshold (catching everything, then manually reviewing flagged items), while routine call recordings might use a higher threshold to speed processing.
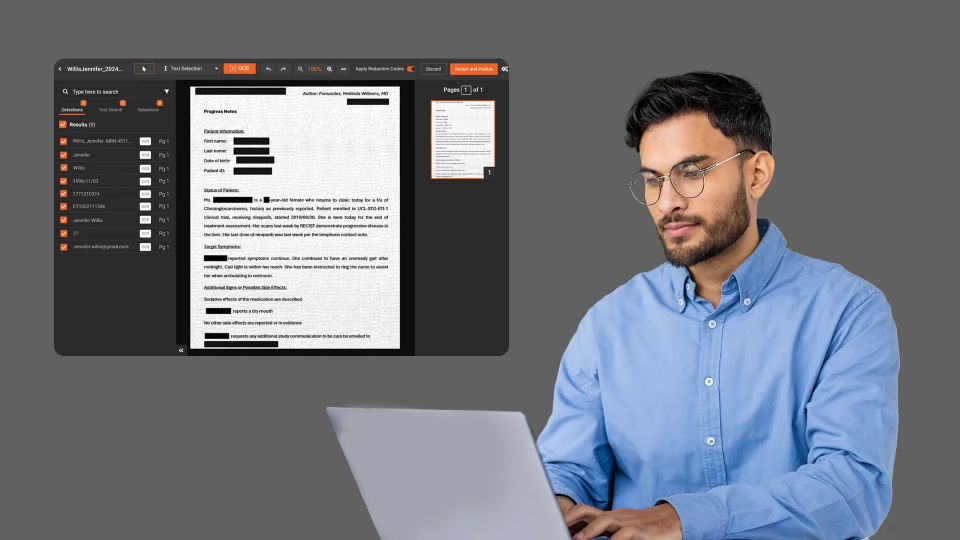
Immutable Audit Trails
HIPAA's Security Rule requires audit controls that record who accessed PHI, what actions they took, and when. For redaction specifically, that means logging every detection, every redaction decision (apply or dismiss), every reviewer who touched the file, and the final output state. These logs should be stored in tamper-proof (WORM-enabled) storage so they can serve as evidence during OCR audits or litigation.
Role-Based Access and Encryption
The redaction platform itself processes PHI, which means it must implement the Security Rule's access control and encryption requirements. Role-Based Access Control (RBAC), Single Sign-On (SSO), Multi-Factor Authentication (MFA), and AES-256 encryption at rest with TLS encryption in transit are minimum requirements. The platform vendor should also sign a Business Associate Agreement.
How VIDIZMO Redactor Supports HIPAA-Compliant Redaction
VIDIZMO Redactor is an AI-powered redaction platform built to handle PHI across documents, images, video, audio, and DICOM medical imaging files in a single workflow. For healthcare organizations, clinical trial sponsors, and their business associates, it addresses the specific challenges that make multimedia PHI protection so difficult.
Redactor detects 40+ PII and PHI types automatically, including patient names, dates of birth, medical record numbers, physician identifiers, Social Security numbers, and health plan beneficiary numbers. Detection works across printed text via OCR (including handwritten content through Intelligent Character Recognition), spoken language via transcription in 82 languages with speaker diarization, and visual content (faces, name bands, and identifying features in video frames).
For clinical trial and surgical video use cases, DICOM medical imaging support enables redaction of PHI embedded in imaging metadata and overlays without degrading the clinical content.
Ready to see how AI-powered redaction protects PHI across documents, video, audio, and medical imaging?
Start your free Redactor trial
Workflow Modes for Different Risk Levels
The platform supports three operational modes: fully automated (for bulk processing of routine recordings), semi-automated with human review (for high-stakes clinical documents), and manual (for targeted redaction of specific items). Configurable confidence thresholds let compliance teams tune the balance between catch-all detection and efficient processing. A managed redaction service with dual QA review is also available for organizations that need external capacity with clinical-grade quality assurance.
Compliance Infrastructure
Redactor supports HIPAA-compliant deployments, with BAA and Data Processing Agreement (DPA) options for covered entities and business associates. The platform provides AES-256 encryption at rest, TLS encryption in transit, RBAC, SSO, MFA, and immutable audit logs stored in tamper-proof WORM storage. Every redaction action is logged with user ID, IP address, timestamp, and action type, creating the defensible audit trail that OCR auditors expect.
Deployment options include SaaS, government cloud, private cloud, on-premises, and hybrid configurations. That flexibility matters for healthcare organizations with strict data residency requirements or air-gapped environments.
What Are Common HIPAA Redaction Scenarios in Healthcare?
How Do Clinical Research Organizations Prepare Trial Documents?
Contract Research Organizations (CROs) routinely process thousands of pages per engagement. Patient consent forms, lab reports, adverse event narratives, and investigator brochures all contain PHI that must be removed before submission to regulatory bodies or research partners. Batch processing capabilities that handle multiple file types in a single queue, rather than requiring separate workflows for PDFs and images, can reduce processing time from weeks to days.
How Should Organizations Redact Telehealth Recordings?
Telehealth visits generate video recordings where patients state their names, dates of birth, medication lists, and symptoms verbally, while their faces and home environments are visible on camera. Redacting these recordings requires both audio PII detection (to mute or bleep spoken identifiers) and visual AI (to obscure faces and any visible documents in the frame). Processing these elements in parallel within one platform eliminates the risk of sharing a recording where the audio is clean but a patient's face is still visible.
How Do Health Insurers Handle Claims File Redaction?
Health insurers handle claims files containing diagnosis codes, treatment records, provider identifiers, and patient financial information. When these files must be shared with auditors, reinsurers, or legal counsel, targeted redaction ensures that only the information relevant to the recipient's purpose is disclosed. Partial redaction capabilities (redacting specific digits of an SSN or account number) preserve data utility while satisfying HIPAA's minimum necessary disclosure requirements.
How Does HIPAA Apply to Emerging Data Types?
HIPAA was written in 1996, but its broad definition of PHI means it applies to data types that didn't exist when the law was enacted. Wearable health devices, remote patient monitoring feeds, AI-generated clinical summaries, and genomic data all fall under HIPAA's protection requirements if they contain individually identifiable health information.
For redaction teams, this expanding scope means the volume and variety of content requiring PHI removal will only grow. Organizations that rely on manual processes or single-format tools will face increasing backlogs. Those with automated, multi-format redaction capabilities will be better positioned to keep pace.
The Office of the National Coordinator for Health IT (ONC) continues to publish guidance on how emerging technologies intersect with HIPAA requirements, making it a key resource for compliance teams tracking regulatory changes.
People Also Ask
HIPAA is a U.S. law that protects patient health information. It applies to healthcare providers, health plans, clearinghouses, and their business associates such as cloud vendors and billing services.
They include names, detailed geographic data, dates except year, contact info like phone and email, IDs such as SSN and medical records, device and vehicle IDs, URLs and IPs, biometrics, photos, and other unique identifiers. Removing all 18 meets Safe Harbor de-identification.
Redaction removes identifiable data from text, images, audio, and video. Properly de-identified data is no longer subject to HIPAA restrictions, allowing safe sharing and analysis.
Masking replaces structured data with realistic substitutes for testing. Redaction permanently removes sensitive data from unstructured content like documents, audio, and video.
Yes. AI tools detect PHI across formats using OCR, speech recognition, and computer vision. For high-risk use cases, human review is recommended to ensure accuracy.
It triggers HIPAA’s Breach Notification Rule. Organizations must notify affected parties within 60 days and may face fines and reputational damage.
HIPAA focuses on PHI protection in healthcare. FOIA applies to public records and uses legal exemptions. Some organizations must comply with both.
About the Author
Ali Rind
Ali Rind is a Product Marketing Executive at VIDIZMO, where he focuses on digital evidence management, AI redaction, and enterprise video technology. He closely follows how law enforcement agencies, public safety organizations, and government bodies manage and act on video evidence, translating those insights into clear, practical content. Ali writes across Digital Evidence Management System, Redactor, and Intelligence Hub products, covering everything from compliance challenges to real-world deployment across federal, state, and commercial markets.
Jump to
You May Also Like
These Related Stories
.jpg)
Why Healthcare SaaS Companies Need Video Redaction
Redacting PHI from ABA Therapy Session Notes: A HIPAA Compliance



No Comments Yet
Let us know what you think